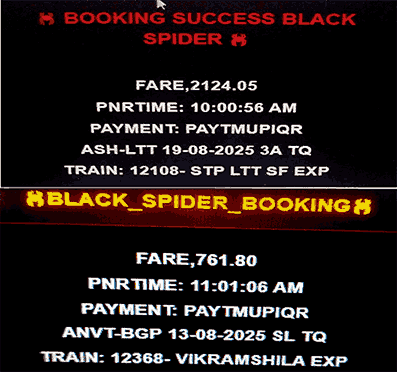
Black Spider Extension
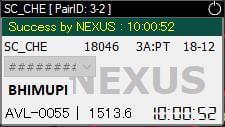
Nexus PRO
TESLA

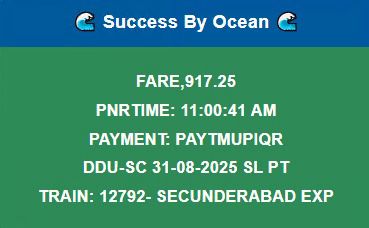
OCEAN EXTENSION
Detection involves identifying patterns in traffic that deviate from normal operational behavior.
Modern Linux systems rely on the Netfilter subsystem within the kernel to handle packet filtering and traffic manipulation. Effective defense-in-depth requires more than just static filtering; it integrates logging with automated analysis tools. Linux Firewalls - Attack Detection and Response...
: A tool that translates Snort intrusion detection rules into equivalent iptables rules using the string match extension to detect application-layer attacks. : A tool that translates Snort intrusion detection
: Implements Single Packet Authorization (SPA) to hide services from unauthorized users, providing a passive authentication layer . Attack Detection Methodologies : The primary utilities for managing firewall rules
: A lightweight daemon that analyzes iptables logs to detect suspicious activity such as port scans, sweeps, and botnet communications.
: The primary utilities for managing firewall rules . They provide strong filtering, Network Address Translation (NAT) , and state tracking.
This write-up explores the methodologies for securing Linux networks using integrated firewall and intrusion detection systems, primarily based on the concepts from by Michael Rash. Core Components of a Linux Security Layer
Happy Super
Best Seller
Best Clients
Happy Users